Bluetooth Printer works with AppleTalk
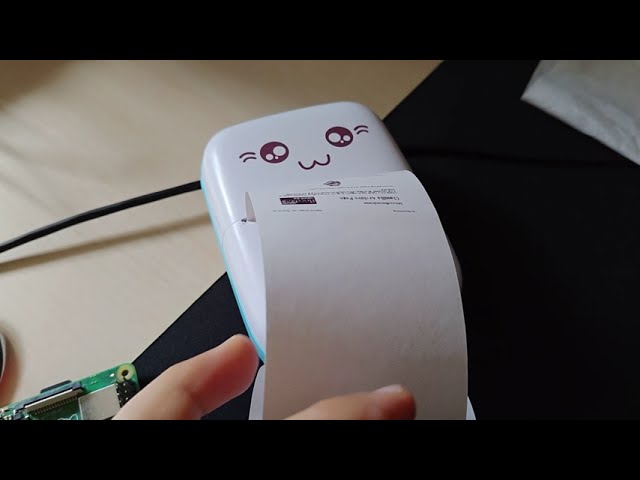
For retrocomputing enthusiasts, getting old computers to work with newer peripherals can be an exciting challenge or horrible headache. If you need to print out receipts from an old Mac, …read more Continue reading Bluetooth Printer works with AppleTalk