S3 Ep138: I like to MOVEit, MOVEit
Backdoors, exploits, and Little Bobby Tables. Listen now! (Full transcript available…) Continue reading S3 Ep138: I like to MOVEit, MOVEit
Collaborate Disseminate
Backdoors, exploits, and Little Bobby Tables. Listen now! (Full transcript available…) Continue reading S3 Ep138: I like to MOVEit, MOVEit

Barracuda’s Email Security Gateway (ESG) has had a vulnerability in it for years. Tracked as CVE-2023-2868, this one was introduced back in version 5.1.3.001, and only got patched during the …read more Continue reading This Week in Security: Barracuda, Zyxel, and The Backdoor
It’s a backdoor, Jim, but not as we know it… here’s a sober look at this issue. Continue reading Researchers claim Windows “backdoor” affects hundreds of Gigabyte motherboards
A backdoor feature found in hundreds of Gigabyte motherboard models can pose a significant supply chain risk to organizations.
The post Organizations Warned of Backdoor Feature in Hundreds of Gigabyte Motherboards appeared first on SecurityWeek.
Continue reading Organizations Warned of Backdoor Feature in Hundreds of Gigabyte Motherboards
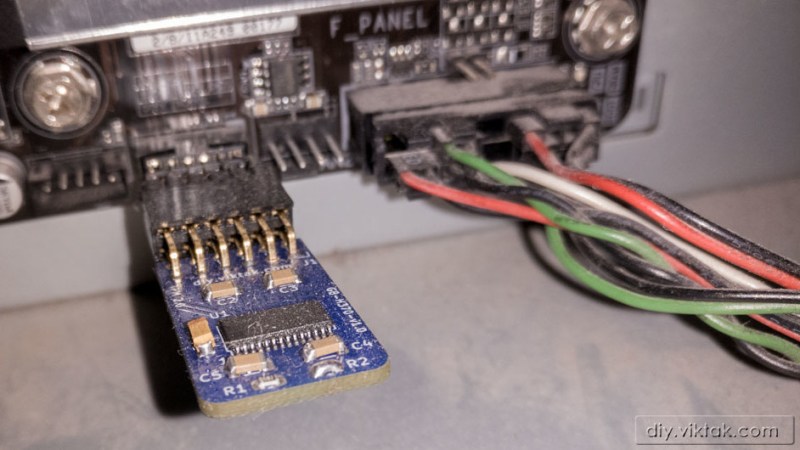
Since Windows 11 has announced its TPM module requirement, the prices for previously abundant and underappreciated TPM add-on boards for PC motherboards have skyrocketed. We’ve been getting chips and soldering …read more Continue reading TPM Module Too Expensive? DIY Your Own Easily!
A curious trend for some years in the world of PC hardware has been that of attaching LEDs to all the constituent parts of a computer. The idea is that somehow a gaming rig that looks badass will somehow be just a little bit faster. As [Graham Sutherland] discovered when …read more
Dozens of insecure drivers from 20 vendors illustrate widespread weaknesses when it comes to kernel protection. Continue reading Driver Disaster: Over 40 Signed Drivers Can’t Pass Security Muster
Hey, you know what’s happening right now? We’re wrapping up the third round of The Hackaday Prize. This challenge, Wheels, Wings, and Walkers, is dedicated to things that move. If it’s a robot, it qualifies, if it’s a plane, it qualifies, if it passes butter, it qualifies. There’s only a short time for you to get your entry in. Do it now. Superliminal advertising.
Speaking of the Hackaday Prize, this project would be a front-runner if only [Peter] would enter it in the competition. It’s one thing to have a cult; I have a cult and a petition to …read more
At this year’s BlackHat Asia security conference, researchers from Cylance disclosed two potentially fatal flaws in the UEFI firmware of Gigabyte BRIX small computers which allow a would-be attacker unfettered low-level access to the computer.
Gigabyte has been working on a fix since the start of 2017. Gigabyte are preparing to release firmware updates as a matter of urgency to only one of the affected models — GB-BSi7H-6500 (firmware vF6), while leaving the — GB-BXi7-5775 (firmware vF2) unpatched as it has reached it’s end of life. We understand that support can’t last forever, but if you sell products with such …read more
![]() Continue reading Gigabytes the Dust with UEFI Vulnerabilities
Continue reading Gigabytes the Dust with UEFI Vulnerabilities
GIGABYTE BRIX UEFI firmware for the GB-BSi7H-6500 and GB-BXi7-5775 platforms,versions vF6 and vF2 respectively,fails to properly set the BIOSWE,BLE,SMM_BWP,and PRx bits to enforce write protection. It also is not cryptographically signed. These issues may permit an attacker to write arbitrary code to the platform firmware,potentially allowing for persistent firmware level rootkits or the creation of a permanent denial of service condition in the platform. Continue reading VU#507496: GIGABYTE BRIX UEFI firmware fails to implement write protection and is not cryptographically signed