Safety from Pixelscan detector on Gologin [closed]
How can I keep my proxy from being detected by Pixelscan on Gologin?
Continue reading Safety from Pixelscan detector on Gologin [closed]
Collaborate Disseminate
How can I keep my proxy from being detected by Pixelscan on Gologin?
Continue reading Safety from Pixelscan detector on Gologin [closed]
By Uzair Amir
Stay up to date on the ever-changing trends and enhance your internet security with traditional VPNs. Not only do they provide an extra layer of protection, but they also come with plenty of entertainment credentials!
This is a post from … Continue reading VPN Evolution: Security and Entertainment Essentials Amid Rising Digital Risks
By Uzair Amir
Just as surfing the web is better with a stable internet connection, completing tasks like web scraping or…
This is a post from HackRead.com Read the original post: Diving Into Stability: How Static Proxies Transform Online Experience
Continue reading Diving Into Stability: How Static Proxies Transform Online Experience
By Uzair Amir
VPN or Residential Proxies: Which is best? Let’s explore without diving into technical details.
This is a post from HackRead.com Read the original post: Exploring the Differences Between Residential Proxies and VPNs: Which is Right for You?
Continue reading Exploring the Differences Between Residential Proxies and VPNs: Which is Right for You?
So, our proxy server blocks all traffic except approved ones.
Would allowing a URL shortening (aka.ms, for example) mean any URL will bypass the proxy? Or is it just a redirect and the proxy/security system inspects the original URLs (whit… Continue reading In general, is URL shortening safe when used with proxy server?
My website has hundreds of thousands of html pages that are open to public. Each time a html page is requested, a call will be made to my database to get the correct data. Therefore the cost of each html request is not cheap (a call to dat… Continue reading How to prevent spam attacks from rotating proxies
My website has hundreds of thousands of html pages that are open to public. Each time a html page is requested, a call will be made to my database to get the correct data. Therefore the cost of each html request is not cheap (a call to dat… Continue reading How to prevent spam attacks from rotating proxies
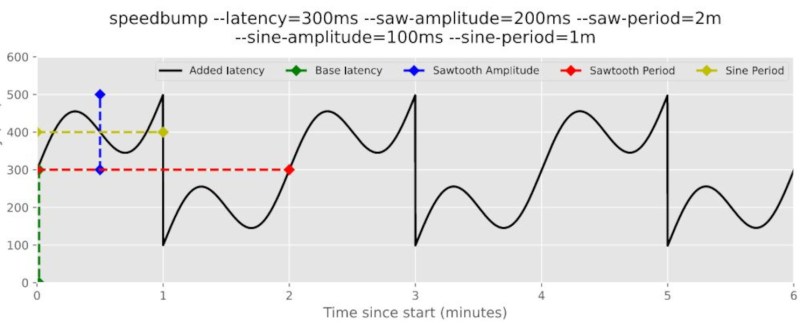
The selfhosting community is an interesting and useful part of the Internet dedicated to removing one’s own services and data from the cloud and hosting it on their own servers, …read more Continue reading Modeling Network Latency
A brief schema of a TLS intercepting proxy – the Client connects to the Host via the Proxy in a way which allows the Proxy to perform a (consensual) MITM.
[Client] -> [Proxy] -> [Host]
It’s my understanding reading references on… Continue reading Does TLS interception necessarily require a self-signed certificate? Please explain why
I want to limit access from the Internet to my Web server but the clients will have a dynamic IP address so the best I can do is to whitelist all addresses belonging to that specific mobile carrier which still leaves the system open to too… Continue reading Can a Reverse Proxy be used instead of port filtering?