Amazon Neptune: 6 Ways to Use the AWS Graph Database
Learn how you can use Amazon Neptune’s Graph Database to simplify building and running graph applications. Continue reading Amazon Neptune: 6 Ways to Use the AWS Graph Database
Collaborate Disseminate
Learn how you can use Amazon Neptune’s Graph Database to simplify building and running graph applications. Continue reading Amazon Neptune: 6 Ways to Use the AWS Graph Database
Database admins strive to ensure that large chunks of data are both accessible and stored with integrity. By using these programming languages, they can keep systems optimized. Continue reading 5 programming languages database administrators should learn
By Waqas
The owner and administrator of the Illicit Services OSINT Tool cites the rise in illegitimate activities and exploitation as reasons for closure.
This is a post from HackRead.com Read the original post: OSINT Tool ‘Illicit Services’… Continue reading OSINT Tool ‘Illicit Services’ Shuts Down Amidst Exploitation Concerns
By Deeba Ahmed
Two groups of threat actors, namely CYBO CREW and UNIT8200, are apparently selling the same database with a price tag of $3,000.
This is a post from HackRead.com Read the original post: Threat Actors Selling 1.8TB Database of Indian Mobi… Continue reading Threat Actors Selling 1.8TB Database of Indian Mobile Users
According to NBC News, the FBI created a national online database in May to facilitate information sharing between hundreds of police departments and law enforcement agencies across the country pertaining to swatting incidents. From the report: No cent… Continue reading FBI Forms National Database To Track and Prevent ‘Swatting’
20 miles west of Portland, engineers at an Intel lab are dunking expensive racks of servers “in a clear bath” made of motor oil-like petrochemicals, reports the Oregonian, where the servers “give off a greenish glow as they silently labor away on ordin… Continue reading Will Submerging Computers Make Data Centers More Climate Friendly?
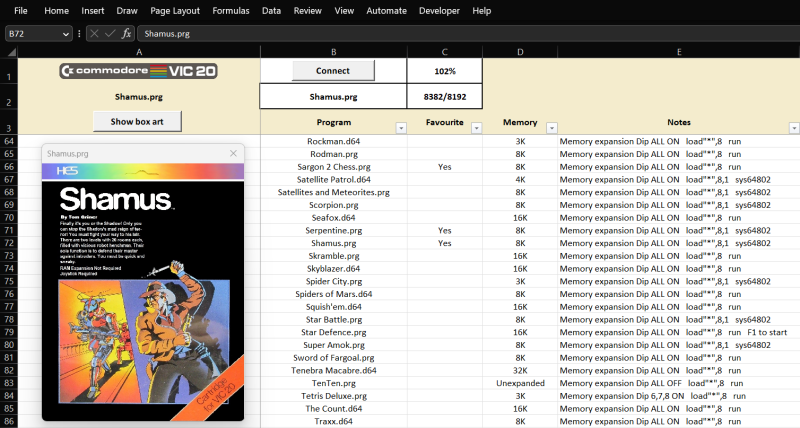
The “save” icon for plenty of modern computer programs, including Microsoft Office, still looks like a floppy disk, despite the fact that these have been effectively obsolete for well over …read more Continue reading Using Excel to Manage a Commodore 64
By Waqas
Scrubs & Beyond were alerted multiple times about the data leak, but the company did not respond or secure the server.
This is a post from HackRead.com Read the original post: Scrubs & Beyond Leaks 400GB of User PII and Card Data in P… Continue reading Scrubs & Beyond Leaks 400GB of User PII and Card Data in Plain Text
By Waqas
ChatGPT’s capabilities have been put to the test in numerous ways, and it has successfully passed no less than four U.S. benchmarking examinations for physicians.
This is a post from HackRead.com Read the original post: ChatGPT Can Vastly Impr… Continue reading ChatGPT Can Vastly Improve Healthcare, But The Industry Needs A Secure Database First
Computer science researchers at MIT and Stanford are developing an operating system with built-in cybersecurity defenses.
The post MIT and Stanford researchers develop operating systems with one major promise: Resisting ransomware appeared first on CyberScoop.