Introduction
There’s a Reddit post today with a PSA (Public Service Announcement) about Crunchyroll, a website that offers anime streaming, being hacked:
PSA : Don’t enter crunchyroll.com at the moment, it seems they’ve been hacked.
As mentioned before, Crunchyroll offers anime streaming, and in their own words:
Enjoy your favorite anime & manga at the speed of Japan
The German Crunchyroll team has additionally issued the following warning:
And for our English-speaking audience
Please DO NOT access our website at the current time. We are aware of the issues and are working on it
— Crunchyroll.de (@Crunchyroll_de) November 4, 2017
The official CrunchyRoll Twitter account has tweeted the following:
ATTENTION ALL CRUNCHYROLL USERS!!
Please DO NOT access our website at the current time. We are aware of the issues and are working on it!!
— Crunchyroll (@Crunchyroll) November 4, 2017
If you are only interested in how to remove this malware, scroll down to the disinfection/removal section.
Update: CrunchyRoll has announced, after a few hours, that the issue is resolved:
— Crunchyroll (@Crunchyroll) November 4, 2017
However, I still advise you to scroll over to the disinfection or removal section. Any questions, feel free to leave a comment, or contact me on Twitter.
Analysis
So, what happens when you visit the CrunchyRoll website? Curently, you get a message the website has encountered an error:
 |
| Figure 1 – CrunchyRoll error page |
Earlier today, the CrunchyRoll website was showing the following:
While the CrunchyRoll team claims it was a DNS hijack, I have (so far) found no evidence as to the validity of this claim, and it rather appears someone was able to hack the website.
Either way, while this is bad, CrunchyRoll took swift action by taking down the website, and an investigation is under way.
What happens if you click the ‘Download now’ button? A new file, called CrunchyViewer.exe, will be downloaded from the following IP address:
109.232.225[.]12
This IP appears to have hosted fake antivirus software or similar in the past:
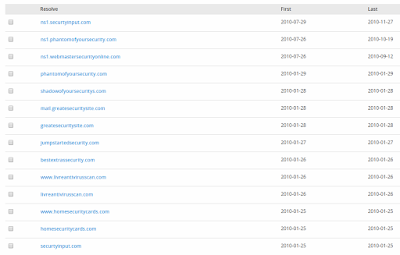 |
| Figure 3 – Older resolutions (2010) |
The newly download file is seemingly the legitimate CrunchyViewer or Crunchyroll, but, near the end of the file, there is a chunk of Base64 encoded data appended, as seen in Figure 4:
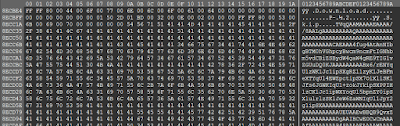 |
| Figure 4 – base64 encoded data (click to enlarge) |
Using a Base64 decoder, we get a new file, called svchost.exe. This binary will place a copy of itself in the current user’s %appdata%\roaming folder, for example:
C:\Users\Yourusername\AppData\Roaming\svchost.exe
This file will periodically call to its C2, or command-and-control server, and wait for any commands:
145.239.41[.]131
Currently, it does not appear the C2 responds on that specific port (6969), however, it is online.
There are claims the malware will additionally install ransomware – I have not observed this behaviour, but it is definitely possible once the C2 sends back (any) commands. More likely, it is a form of keylogger – malware that can record anything you type, and send it back to the attacker.
Svchost.exe will also create an autorun entry:
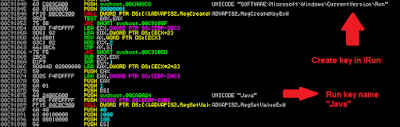 |
| Figure 5 – newly created run key (click to enlarge) |
This basically means the malware will start every time you (re)boot or restart the machine.
Just for fun, it appear that the miscreant’s name, or the person responsible for creating the malware is named Ben, as appears from the debug paths:
C:\Users\Ben\Desktop\taiga-develop\bin\Debug\Taiga.pdb
c:\users\ben\source\repos\svchost\Release\svchost.pdb
Taiga is ‘A lightweight anime tracker for Windows’. This does not mean they are involved, but rather that ‘Ben’ has decided to include Taiga in the package.
Update: the developer of Taiga has included a fix for ‘CrunchyViewer’:
https://github.com/erengy/taiga/issues/489
Disinfection/Removal
Disinfection is rather straightforward:
- Remove the malicious “Java” Run key, by opening Regedit, and browsing to:
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
- Delete the ‘Java‘ key;
- Remove the malicious binary, by navigating to:
%appdata%\Roaming (for example: C:\Users\Yourusername\AppData\Roaming\)
- Delete the ‘svchost.exe’ file.
- Perform a scan with your installed antivirus product;
- Perform a scan with an online antivirus, which is different from the one you have. Alternatively, perform a scan with Malwarebytes.
- Change all your passwords if possible. Better be safe than sorry.
Prevention
Prevention advise in general, which also pertains to CrunchyRoll’s compromise:
- Install an antivirus;
- Keep your browser up-to-date;
- Install NoScript if you have Firefox;
- Install a ‘well-rounded’ ad-blocker, for example uBlock Origin (works with most browsers);
- If a website you visit frequently suddenly looks completely different, or urges you to download whatever, be safe rather than sorry, and leave the website.
- Additionally, try to Google or use social media to verify if anyone else is experiencing the same issue.
Conclusion
This hack shows that any website or organisation is, in theory, vulnerable to someone hijacking the website, and consequently download and install malware on a user’s machine.
While it is uncertain what exactly happened, CrunchyRoll took correct action by taking the website down not too long after. At this point, it is best to monitor their Twitter account, and/or wait for an official statement.
If you have not executed the file, you should be safe. Follow the prevention tips above to stay secure.
IOCs
The post CrunchyRoll hack delivers malware appeared first on Security Boulevard.
Continue reading CrunchyRoll hack delivers malware→