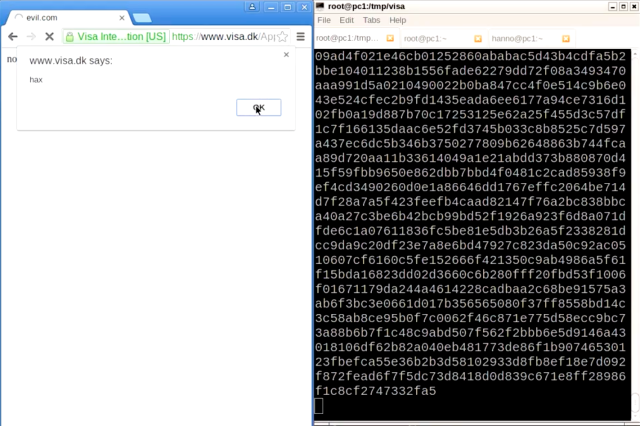
Enlarge (credit: Hanno Böck)
Dozens of HTTPS-protected websites belonging to financial services giant Visa are vulnerable to attacks that allow hackers to inject malicious code and forged content into the browsers of visitors, an international team of researchers has found.
In all, 184 servers—some belonging to German stock exchange Deutsche Börse and Polish banking association Zwizek Banków Polskich—were also found to be vulnerable to a decade-old exploit technique cryptographers have dubbed the “forbidden attack.” An additional 70,000 webservers were found to be at risk, although the work required to successfully carry out the attack might prove to be prohibitively difficult. The data came from an Internet-wide scan performed in January. Since then, Deutsche Börse has remedied the problem, but, as of Wednesday, both Visa and Zwizek Banków Polskich have allowed the vulnerability to remain and have yet to respond to any of the researchers’ private disclosures.
The vulnerability stems from implementations of the transport layer security protocol that incorrectly reuse the same cryptographic nonce when data is encrypted. TLS specifications are clear that these arbitrary pieces of data should be used only once. When the same one is used more than once, it provides an opportunity to carry out the forbidden attack, which allows hackers to generate the key material used to authenticate site content. The exploit was first described in comments submitted to the National Institute of Standards and Technology. It gets its name because nonce uniqueness is a ground rule for proper crypto.