Don’t Fret Over the Ukulele
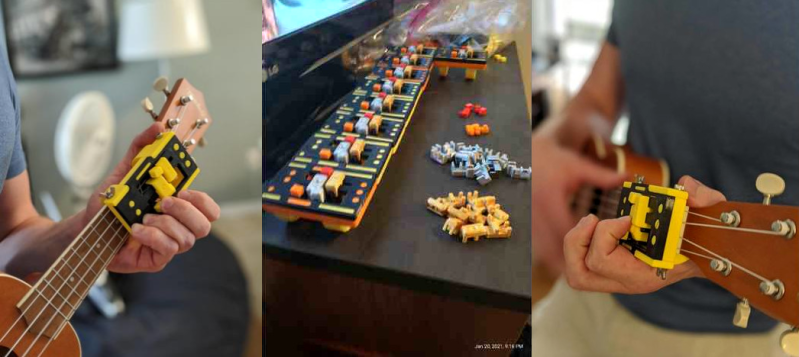
A ukulele is a great instrument to pick to learn to play music. It’s easy to hold, has a smaller number of strings than a guitar, is fretted unlike a …read more Continue reading Don’t Fret Over the Ukulele
Collaborate Disseminate
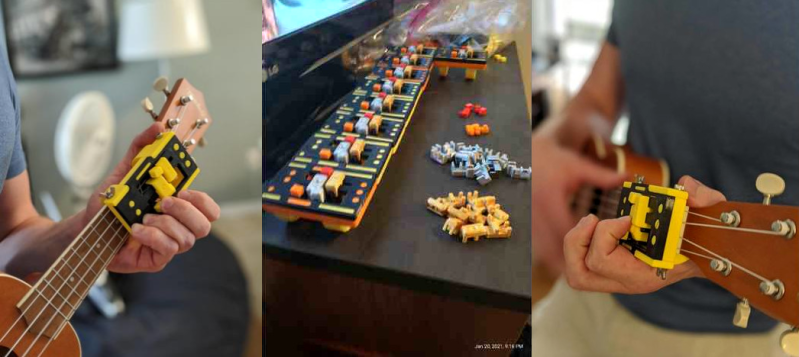
A ukulele is a great instrument to pick to learn to play music. It’s easy to hold, has a smaller number of strings than a guitar, is fretted unlike a …read more Continue reading Don’t Fret Over the Ukulele
Joshua Vasquez wrote a piece a couple of weeks ago about how his open source machine benefits greatly from having part numbers integrated into all of the 3D printed parts. It lets people talk exactly about which widget, and which revision of that widget, they have in front of them. …read more
From an answer to the question RSA maximum bytes to encrypt, comparison to AES in terms of security? I learned that there is a theoretical limit of how much data can be safely encrypted with symmetric block ciphers (like AES for example) w… Continue reading Is there a maximum number of encryptions I should make with the same RSA key? [migrated]
I’m curious if the origin of any successful computer virus is known to NOT have an intentional, human originator. To put it another way, do computer viruses ever “spontaneously” originate through the process of natural selection in the sa… Continue reading Are all computer viruses man-made?
I created a sort of theoretical attack but I’ve a question about identification.
Requirements:
Site that requires logged-in user + phone verify to reset the password.
Site that sends SMS fast, less than 2 minutes.
and on the Attacker’… Continue reading Identification in a user-to-mass phishing attack
Does one have the official theory how did Mitnick afford himself to get Shimomura his IP addres?
Continue reading How did Mitnick knew Shimomura his IP addres? [closed]
Does one have the official theory how did Mitnick afford himself to get Shimomura his IP addres?
Continue reading How did Mitnick knew Shimomura his IP addres? [closed]
I have a fundamental theory question. Is looking for cross-site scripting a solved computer science problem? Or is it an open problem? Does it approximate the halting problem, injection problem or similar known CS problems?
Or is XSS not … Continue reading Is ‘looking for all XSS in my code’ a solved computer science problem?
Building a general-purpose computer means that you’ll have to take a lot of use cases into consideration, and while the end product might be useful for a lot of situations, it will inherently contain a lot of inefficiencies. On the other hand, if you want your computer to do one …read more
I’m learning about security, and it seems that all of the security problems I have seen come from input from malicious actors.
I was told that it’s possible to check for the existence of bugs in a program, but not possible t… Continue reading Can a program that doesn’t explicitly take user input be hacked?