Running DOOM on…a TrueType Font?
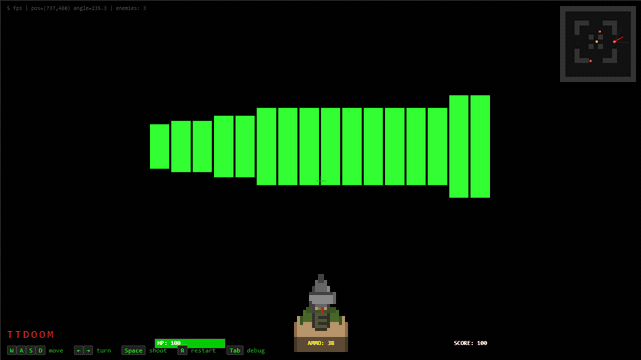
Over the years, DOOM has been ported to many things; think of any arbitrary device and chances are it can run the classic shooter. But what about something more esoteric …read more Continue reading Running DOOM on…a TrueType Font?
