The last decade has taught us much about computer and information security. We’ve learned the importance of Secure-By-Default because people rarely harden their “security” settings as standard practice. We’re also painfully aware that security is often a trade-off between functionality and usability, which requires a balance be made. Ideally this balance is decided between what level of security a product claims and the customer’s expectations. Operating systems and Web servers have taken a strong supporting stance with regards to Secure-By-Default. Web browsers, well, I think there is much room for improvement.
Let’s look at recent outcomes shall we. According to CA Technologies, “Browser-based exploits accounted for 84% of the total actively exploited known vulnerabilities in the wild.” Other industry reports support these findings including, “Of the top-attacked vulnerabilities that Symantec observed in 2009, four of the top five being exploited were client-side vulnerabilities that were frequently targeted by Web-based attacks.” 2010 wasn’t much different. This is typically the result of a combination of imperfect software and not keeping browsers & plug-in patches up-to-date.
Even in this context the browser vendors (Google, Microsoft, and Mozilla) should still be given a lot credit for having been vastly improved the overall security of their software in the last two or so years. They have better development practices, publish regular and timely patches, included easy scheduled update mechanisms, added anti-malware/phishing features, sandboxes, and bounty programs. Collectively speaking anyway, but that’s where it ends. All great benefits that users receive automatically and/or enabled by default. That is, Secure-By-Default. Memory handling issues aside, where these protections mainly focus, are still many extremely devastating attack classes where users have practically zero ability to defend themselves.
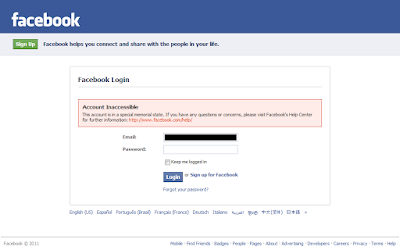
I’m talking about Intranet Hacking, DNS Rebinding, Clickjacking (UI Redressing), Cross-Site Scripting, Cross-Site Request Forgery, CSS History Leaks, and WiFi Man-in-the Middle. I see these as being the most pressing. They break the back of the Same-Origin-Policy, the very foundation of browser security, and there’s evidence that most of these have been used maliciously in the wild. A malicious website can easily detect what websites a visitor is logged-in to, what sites they’ve recently visited, take over their online bank/email/socialnetwork/etc accounts, hack into their DSL router or corporate intranet. Or maybe the attacker wants to get the victim in legal trouble by forcing them to attack other systems, post spam, download illegal content, and so on.
Sure, an individual user can defend themselves with add-ons like NoScript, Adblock Plus, LastPass, Better Privacy and so on, of which I’m a fan and user. To reiterate though, this is in no way a demonstration of Secure-by-Default! Users have to first be aware, download the application, install, and finally configure. The reality is most users don’t know these attackers are possible and even easy to perform. Only the readers of this blog and the browser vendors themselves do. So from a 10,000ft view of Web security, if a protection feature is not enabled by default then it doesn’t matter. Case in point…
To combat these issues, keep the security-minded elite mildly happy, and show that “something” is being done, there’s a mile long list of well intentioned security features that extremely few people outside of out tiny Web security sphere have heard of let alone implemented. HTTP Strict Transport Security, SECURE cookie flag, httpOnly cookies, X-FRAME-OPTIONS header, Origin header, Do-Not-Track header, disable form AutoComplete, iFrame security restriction, Content Security Policy, privacy modes, hidden configuration settings, delete browser data, cookie controls, LSO controls, etc. All of these are opt-in, invisible or buried several mouse-clicks deep in the GUI, and likely implemented differently. No wonder “The Need for Coherent Web Security Policy Framework(s)” was published.
There are lots of competing arguments about why these things haven’t been or shouldn’t be formally adopted. My intention here is not to rehash those, but instead remind us all about the bigger picture. I mean, it is simply amazing how much we are able to do online with just a browser. We can shop, bank, pay bills, file taxes, share photos, keep in touch with friends and family, watch movies, play games, and so much more. Browsers are the most important connection we have to the Internet. And the “we” is a stunning two billion people strong. Clearly browsers play a vital role in online security. Everyone needs a Web browser that is not only fast and stable, but secure as well. Only it is difficult to say that they are (or have been)… secure. That needs to change, somehow, someway, and preferably soon.
Continue reading Web Browsers and Opt-In Security→
 Window of Exposure is an organizational key performance indicator that measures the number of days a website has at least one serious vulnerability over a given period of time.
Window of Exposure is an organizational key performance indicator that measures the number of days a website has at least one serious vulnerability over a given period of time.