What’s the strategy one should use when trying to defend an organization against the threats we face today. At times the security strategy has been reactive. Decisions and the direction forward are based on the latest incident the organization experienced. This approach is not effective since it is the equivalent of firefighting where resources are used on addressing the latest fire without identifying the underlying issues causing the fires in the first place. At other times the security strategy is based on compliance. Decisions and the direction forward are based on regulations or standards the organization has to be compliant with. This approach is not as effective either. It will provide an organization with some minimum security controls but it may not help with defending against the threats we face today (the news highlights organizations who are compliant but are still compromised anyway). One security strategy that has gained traction over the years and is more effective than the previous two is intelligence driven security. The direction forward and “decisions are made based on real-time knowledge regarding the cyber adversaries and their attack methods, and the organization’s security posture against them”. This approach is more effective than the previous two since it enables an organization to allocate security resources to address the highest risks and threats they face.
In this post, I sharing linkz to various resources I found useful over the past few years related to the intelligence driven security, threat intelligence, threat intelligence data, consuming threat intelligence data, and threat intelligence sharing.
Intelligence Driven Security Links
These links are related to intelligence driven security, which RSA defined as “developing real-time knowledge on threats and the organization’s posture against those threats in order to prevent, detect, and/or predict attacks, make risk decisions, optimize defensive strategies, and enable action.”
Achieving Intelligence-Driven Information Security
The first link is one that will always hold a certain personal value since it was one of the first papers I read on the topic years ago. The RSA paper Getting Ahead of Advanced Threats: Achieving Intelligence-Driven Information Security discusses how an organization can approach managing their security program in this manner. The paper addresses: what organizations need to know, categories of cyber-risk data, intelligence driven information security, roadmap to achieving intelligence driven information security, opportunities for quick wins, and information sharing. I spent years performing vulnerability assessments against other organizations and each engagement it became more and more clear that the traditional approaches to security management were no longer effective. What was needed was an approach were factual information influenced decisions instead of decisions being based solely on someone’s judgment or gut feeling. The approach in this paper is very light on details but it does address the thought process behind it and to me this was very helpful. The paper did nail the foundation one needs to have in place to achieve this as seen in the following quote: “to be ready to take on an intelligence program, the organization needs to have a foundation in place for monitoring the network for intrusions and a workflow process for responding to incidents.”
Strategic Cyber Intelligence
The reason behind leveraging intelligence in security management is to help people make better security decisions. These decisions can be related to addressing risks, security strategies, and resource usage. Despite this being the driving force behind intelligence driven security a good percentage of the material I’ve seen on the topic is more focused on the real time intelligence about threats and not about the intelligence an organization needs to make better security decisions. The next link I picked up from Richard Bejtlich and it’s a document titled Strategic Cyber Intelligence. If there is only one link to read in this post then this document is it. My words wouldn’t do justice in describing this document so instead I’m opting to use part of the executive summary to describe it.
While there has been much emphasis on tactical cyber intelligence to help understand the “on-the-network” cyber-attacks so frequently in the news, there has been little discussion about the strategic and operational levels in order to better understand the overall goals, objectives, and inter-relationships associated with these tactical attacks. As a result, key consumers such as C-suite executives, executive managers, and other senior leaders are not getting the right type of cyber intelligence to efficiently and effectively inform their organizations’ risk management programs. This traditionally tactical focus also hampers the capability of the cyber intelligence function to communicate cyber risks in a way that leaders can fully interpret and understand.
Adopting Intelligence Driven Security
The next links I found helpful since they had some good talking points and a nice diagram to get buy-in to approach security in a more intelligent manner. The RSA Adopting Intelligence Driven Security paper provides a high-level overview about adopting an intelligence driven security strategy. Topics discussed include: visibility, analysis, action, and difference between today’s security strategies and intelligence driven. The RSA blog post What is Intelligence Driven Security? provides very similar but less information than their paper.
Threat Intelligence Links
Threat intelligence is a needed component in achieving intelligence driven security but the two are not the same. This can be seen in the iSightPartners threat intelligence definition, which is “cyber threat intelligence is knowledge about adversaries and their motivations, intentions, and methods that is collected, analyzed, and disseminated in ways that help security and business staff at all levels protect the critical assets of the enterprise”. These links provide information about threat intelligence.
Threat intelligence: Collecting, Analysing, and Evaluating
The MWR InfoSecurity Threat intelligence: Collecting, Analysing, and Evaluating whitepaper provides an excellent overview about threat intelligence and a threat intelligence program. Topics included are: what is threat intelligence, building a threat intelligence program, strategic/operational/tactical threat intelligence, and technical threat intelligence. The paper is well worth taking the time to read since the overview touched on most components of a threat intelligence program.
Definitive Guide to Cyber Threat Intelligence
iSIGHT Partners is a vendor providing threat intelligence services. They released a short ebook titled Definitive Guide to Cyber Threat Intelligence (at the time of this post the link for the PDF is here and if it no longer works then you’ll need to provide them your email address to receive the download link). In their own words the following is why they wrote the book: “We figured that since we wrote the book on cyber threat intelligence, we might as well write the book on cyber threat intelligence”. The book itself is 74 pages and addresses the following: defining cyber threat intelligence, developing threat intelligence requirements, collecting threat information, analyzing and disseminating threat intelligence, using threat intelligence, implementing an intelligence program, and selecting the right threat intelligence partner. The one area where I think this book shines is by outlining the components that a commercial threat intelligence service should have.
Actionable information for Security Incident Response
ENISA released the Actionable information for Security Incident Response document that was “intended as a good practice guide for the exchange and processing of actionable information”. The document discusses some of the following points: properties of actionable information, levels of information, collecting information, preparing information, storing information, analyzing information, and case studies. The document does an outstanding job outlining the characteristics of actionable intelligence as well as a process one could use to process it.
Threat Intelligence for Dummies
Another ebook released by another threat intelligence vendor named Norse is the book Threat Intelligence for Dummies. The book is a short read (52 pages) and touches on the following areas: understanding threat intelligence, gathering threat intelligence, scoring threat intelligence, supporting incident response, threat mitigation, and buying criteria for threat intelligence solutions. The book is another option for those looking for a more general overview about threat intelligence.
Five Steps to Build an Effective Threat Intelligence Capability
The next link is for a Forrester report about building an effective threat intelligence capability. The first half of the report outlines the case for needing a threat intelligence capability while the second half discusses the actual capability. The topics include: intelligence cycle, intelligence disciplines, and five steps to build the intelligence capability. This report is another approach to building the capability and I find it beneficial to see different approaches for accomplishing the same thing. It makes it easier to pick and choose aspects from the various approaches to find what works best for you.
Open Source Threat Intelligence Data Feeds Links
Data about threats, adversaries, and methods they use can be obtained from various sources. One source for regularly updated threat data is from publically available sources. Despite the data being freely available care must be taken in selecting the data feeds to use. For each data feed its characteristics must be evaluated to determine the value added for an organization’s security monitoring and response process. (Side note: consuming as many feed as possible is counterproductive and could actually impede security monitoring.)
Evaluating Threat Intelligence Data Feeds
These links are a bit dated but they are as relevant today as when they were published. David Bianco’s posts The Pyramid of Pain and What Do You Get When You Cross a Pyramid With A Chain? outline an approach to evaluate the value of indicators. The Pyramid of Pain is a versatile model that can be used when not only evaluating indicators in open source threat intelligence feeds but it is also helpful when trying to assess the coverage in a security monitoring program.
Feeds, Feeds, and More Feeds
The next link is a word of caution from Jack Crook about using threat intelligence data feeds. In his post Feeds, feeds and more feeds his provides some food for thought for those looking to start consuming feeds. Below is a very telling quote from his post:
“By blindly alerting on these types of indicators you also run the risk of cluttering your alert console with items that will be deemed, 99.99% of the time, false positive. This can cause your analysts to spend much unneeded time analyzing these while higher fidelity alerts are sitting there waiting to be analyzed.”
Threat Data Feeds
Now with the links about evaluating data feeds and a word of caution out of the way I can now provide links to websites that contain links to publically available sources for threat data. It’s an easy way to provide a wealth of feed options by linking work done by others.
Introducing the Active Threat Search
Critical Stack Bro Intelligence Framework (need to register but it is well worth it)
Collective Intelligence Framework Data Sources
Threat Intelligence Feeds Gathered by Combine
Opensource intel links
uiucseclab cif-configs
Consuming Threat Intelligence Data Links
One of the ENISA actionable information characteristics is ingestibility. Ingestibility is the ability of the organization receiving the data to “consume it painlessly and automatically, including correlating and associating it with other information”. The consumption is what makes the information useful to an organization to identify vulnerabilities, mitigate an ongoing attack, or detecting a new threat.
Leveraging Threat Intelligence in Security Monitoring
Securosis published a decent paper titled Leveraging Threat Intelligence in Security Monitoring. The paper discusses threat intelligence sources (is mostly focused on malware), and the network security monitoring process before going into detail on integrating threat intelligence with the security monitoring process. The part I really liked about the paper is it outlines a process for managing the security monitoring process that consumes threat intelligence and it takes the time to explain each component. Even if an organization doesn’t use this process its helpful to see how someone else approached consuming threat intelligence to see what can be used to improve their security monitoring processes.
How to Use Threat Intelligence with Your SIEM?
The next link is really a bunch of links. Anton Chuvakin is a Gartner analyst who focuses on SIEM, security monitoring, and incident response. His analysis reports requires a Gartner account to access but he does share some of his research on his blog. Anton wrote numerous posts addressing: consuming threat intelligence, threat intelligence, and threat intelligence data. His post How to Use Threat Intelligence with Your SIEM? talks about how SIEMs can consume threat intelligence data for an organization and the post really hits home since this is one way I consume TI data. He also released the following posts related to threat intelligence:
Threat Intelligence
On Internally-sourced Threat Intelligence
Delving into Threat Actor Profiles
On Threat Intelligence Use Cases
On Broad Types of Threat Intelligence
Threat Intelligence is NOT Signatures!
The Conundrum of Two Intelligences!
Threat Intelligence Data
On Threat Intelligence Sources
How to Make Better Threat Intelligence Out of Threat Intelligence Data?
On Comparing Threat Intelligence Feeds
Consumption of Shared Security Data
From IPs to TTPs
McAfee SIEM and Open Source Intelligence Data Feeds
An easy way to consume open source threat intelligence data is by feeding it into a properly configured SIEM and correlating the data across an organization’s logs. The next few links explain one method to accomplish this with the McAfee SIEM (formerly known as Nitro). The SIEM stores intelligence data inside items called watchlists and these watchlists can be dynamically updated with intelligence feeds. The post Creating a Watchlist from Malc0de shows how to accomplish creating a dynamic watchlist to populate it with the Malc0de feed. I populate my dynamic watchlists using a script; there are always different ways to arrive at the same destination. The watchlist containing threat intelligence data can then be used in correlation. The next post SIEM Foundations: Threat Feeds walks you through creating a static watchlist (I don’t recommend this approach with intelligence feeds) followed by showing different ways to use the watchlist.
Splunk and Open Source Intelligence Data Feeds
Different SIEMs are able to consume threat intelligence data in different ways. The previous links were for McAfee SIEM and the next links are for Splunk. The Deep Impact post Splunk and Free Open-Source Threat Intelligence Feeds “is a write-up for integrating some readily available free and open-source threat intelligence feeds and block lists into Splunk”. The thing I really liked about this post was the author not only explained how to perform this integration but he also released a script to help others do the same.
Bro and Open Source Intelligence Data Feeds
To make use of open source intelligence data feeds you don’t need a SIEM technology. All you need is technology that can consume the data feeds you selected. The next link is a great example of that. Critical Stack has put together their Threat Intelligence for The Bro Platform. I don’t use Bro but I find this idea really slick. They set up a portal where you can log-in, review numerous open source intelligence feeds, select the feeds you want, and then create a subscription that gets ingested into Bro. This has really lowered the bar for people to use open source threat intelligence and even if you don’t use Bro the portal is a nice reference for available data feeds.
Threat Intelligence Sharing Link
Approaching intelligence driven security provides an organization with visibility into their environments. Visibility into the threats they face, the actual attacks conducted against their environment, and their security posture to defend against those threats. Not only does intelligence driven security result in the organization consuming external threat intelligence but it enables the organization to develop and maintain their own threat intelligence based on what they are seeing. Internally developed intelligence can be shared with others. The last link is the only one I had for intelligence sharing.
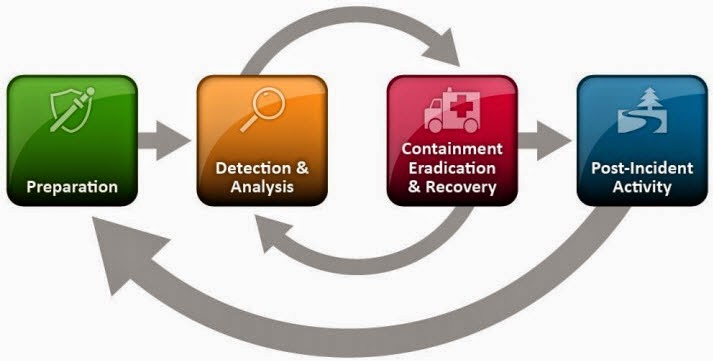
NIST Guide to Cyber Threat Information Sharing
The NIST Special Publication 800-150 Guide to Cyber Threat Information Sharing (in draft format at the time of this post) expands on the NIST Computer Security Incident Handling Guide by exploring “information sharing, coordination, 228 and collaboration as part of the incident response life cycle”. The guide is broken down into the following parts: incident coordination and information sharing overview, understanding current cybersecurity capabilities, establishing, & maintaining, and using information sharing relationships. The guide might be of value for those interested in a more formalized approach to intelligence sharing.
***** 07/01/15 Addendum *****
In response to this post the author of the CYINT Analysis blog pointed me to the threat intelligence resources webpage they put together. The webpage contains additonal resources I didn’t discuss in this post and numerous others I wasn’t aware about. I wanted to update this post to point to the CYINT Analysis resources webpage. Continue reading Linkz for Intelligence Driven Security and Threat Intelligence→