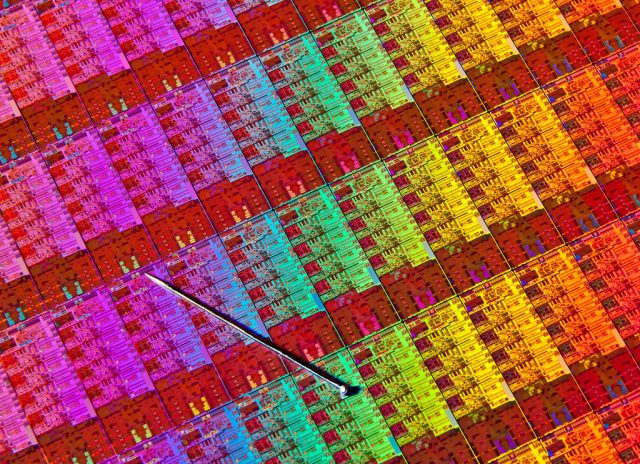
Enlarge / A closeup shot of an Intel Haswell die, with a pin for size reference. (credit: Intel)
Microsoft has released a new Windows patch to disable Intel’s hardware-based mitigation for the Spectre attack due to bugs introduced by Intel’s mitigation.
In the wake of the Spectre and Meltdown attacks that use the speculative execution behavior of modern processors to leak sensitive information, Intel released a microcode update that offers operating systems additional controls over the processor’s ability to predict branches. When paired with corresponding operating system changes, the extra controls can prevent the unwanted information disclosure.
Unfortunately, Intel discovered earlier this month that the microcode updates are causing machines to reboot. Initially this was confirmed to be the case for Haswell and Broadwell chips; Intel later confirmed that it also applied to Sandy Bridge, Ivy Bridge, Skylake and Kaby Lake parts. Intel’s advice was to stop deploying the microcode. A week ago the company said that it had isolated the root cause of reboots, at least for Haswell and Broadwell processors, and that it would soon begin testing a new version.