A remote hijacking flaw that lurked in Intel chips for seven years was more severe than many people imagined, because it allowed hackers to remotely gain administrative control over huge fleets of computers without entering a password. This is according to technical analyses published Friday.
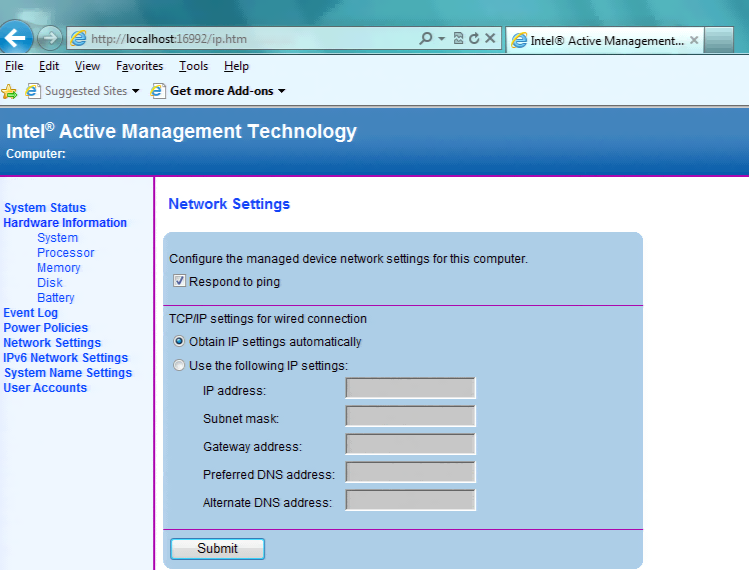
As Ars reported Monday, the authentication bypass vulnerability resides in a feature known as Active Management Technology. AMT, as it’s usually called, allows system administrators to perform a variety of powerful tasks over a remote connection. Among the capabilities: changing the code that boots up computers, accessing the computer’s mouse, keyboard, and monitor, loading and executing programs, and remotely powering on computers that are turned off. In short, AMT makes it possible to log into a computer and exercise the same control enjoyed by administrators with physical access.
AMT, which is available with many vPro processors, was set up to require a password before it could be remotely accessed over a Web browser interface. But, remarkably, that authentication mechanism can be bypassed by entering any text string—or no text at all. According to a blog post published Friday by Tenable Network Security, the cryptographic hash that the interface’s digest access authentication requires to verify someone is authorized to log in can be anything at all, including no string at all.