Google has shut down an operation that combined malicious AdSense advertisements with a zero-day attack exploiting Chrome for Android to force devices to download banking fraud malware.
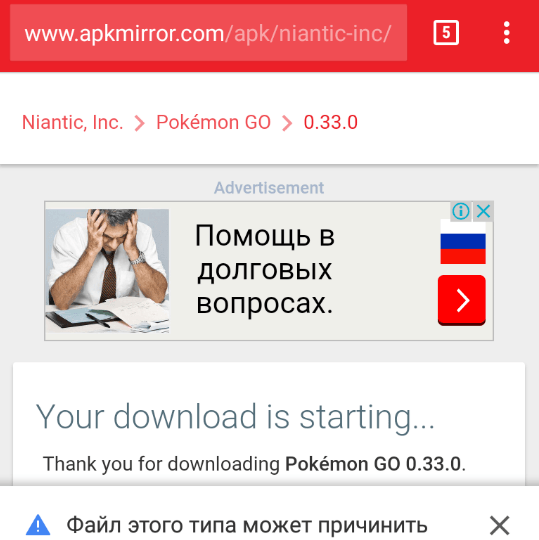
Over a two-month span, the campaign downloaded the Banker.AndroidOS.Svpeng banking trojan on about 318,000 devices monitored by Kaspersky Lab, researchers from the Moscow-based anti-malware provider reported in a blog post published Monday. While the malicious installation files weren’t automatically executed, they carried names such as last-browser-update.apk and WhatsApp.apk that were designed to trick targets into manually installing them. Kaspersky privately reported the scam to Google, and engineers from the search company put an end to the campaign, although the timing of those two events wasn’t immediately clear.
“So far, those behind Svpeng have limited their attacks to smartphone users in Russia,” Kaspersky Lab researchers Nikita Buchka and Anton Kivva wrote in Monday’s post. “However, next time they push their ‘adverts’ on AdSense they may well choose to attack users in other countries; we have seen similar cases in the past. After all, what could be more convenient than exploiting the most popular advertising platform to download their malicious creations to hundreds of thousands of mobile devices?”