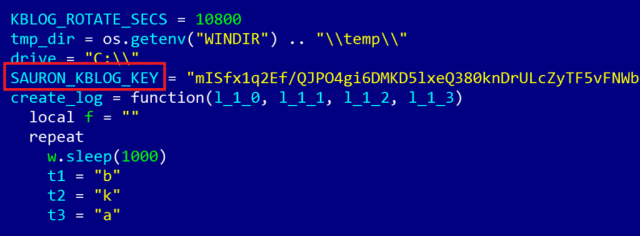
The name “Project Sauron” came from code contained in one of the malware’s configuration files. (credit: Kaspersky Lab)
Security experts have discovered a malware platform that’s so advanced in its design and execution that it could probably have been developed only with the active support of a nation state.
The malware—known alternatively as “ProjectSauron” by researchers from Kaspersky Lab and “Remsec” by their counterparts from Symantec—has been active since at least 2011 and has been discovered on 30 or so targets. Its ability to operate undetected for five years is a testament to its creators, who clearly studied other state-sponsored hacking groups in an attempt to replicate their advances and avoid their mistakes. State-sponsored groups have been responsible for malware like the Stuxnet- or National Security Agency-linked Flame, Duqu, and Regin. Much of ProjectSauron resides solely in computer memory and was written in the form of Binary Large Objects, making it hard to detect using antivirus.
Because of the way the software was written, clues left behind by ProjectSauron in so-called software artifacts are unique to each of its targets. That means that clues collected from one infection don’t help researchers uncover new infections. Unlike many malware operations that reuse servers, domain names, or IP addresses for command and control channels, the people behind ProjectSauron chose a different one for almost every target.